Cyber Tech Ware
Home
- These posts contain affiliate links
- Cyber Tech Ware may earn commision if you use our links to purchase any items
- Thank you for supporting us
- Social Links - @Cybertechware

Tech Spec List
- Lian Li 011 Evo Mid Tower
- Gigabyte Aero Z690 Motherboard
- G.Skill Trident Z Royal 32GB 3600
- Samsung 980 2TB M.2
- Asus ROG Strix RTX 3080 GPU
- Intel i7 12700k CPU
- Corsair Elite Capellix H150i AIO
- Corsair 850w 80 plus gold PSU
- Lian Li Strimer plus v2
- Lian Li AL120 Fans

Tech Loadout List
- Aer Day Sling 3 X-Pac
- Bellroy Key Cover
- Apple Airpods
- Spigen Tough Armor
- Mazer C to C Cable
- Mazer C to Lightning adapter
- Aukey PB-N83s 10000 mAh
- Heroclip
- Google Pixel Phone
- Apple Magsafe wallet
- Popsocket
- Aerogin Mercedes
Ad - Ledger Referral
- Ledger Nano X Red
- Ledger Nano X Purple
The secure gateway to all your crypto needs
Buy, exchange and grow your crypto securely with a Ledger hardware wallet, combined with the Ledger Live app. Its never been easier to keep your crypto safe and accessible.
Get $10 in Bitcoin by using our referral link to get your Ledger crypto hardware wallet today.

Tech Loadout List
- ASUS ROG Strix B760-A
- Intel i5-12600k
- ASUS RTX 3060 Dual OC 8GB
- Corsair Vengeance DDR4 RAM
- 2TB NVMe M.2 SSD
- 850W Corsair RM850
- SIGNATURE L-SHAPED WORKSTATION
- Sanyun SW208 Bookshelf speakers
- RGB XL Mousepad
- Razer Ornata V3 Tenkeyless
- 27inch Samsung Odyssey G3
- PS5 Controller
- PS VR2 Headset
- Pegboard

Tech Loadout List
- Anbernic rg280m retro emulation handheld
- Benchmade mini Griptilian with AWT scales
- Mecarmy SGN3 light
- Victorinox Cadet with brass scales
- Applewatch 3 in a Catalyst case

Limited Edition Consoles
Video game consoles come in many shapes, sizes, and sales tags. The standard price will net you normal consoles and games, but if you spend a bit extra, you get a bit extra.
Collectors editions of games are common, and many include additions such as artbooks, steel CD cases, and even the occasional statue. Collectors editions of consoles, meanwhile, are less common.
Most of the time, limited and collectors edition consoles are well worth the cash, especially if you love the games they come with and their related iconography. However, here are some of the worst collectors edition consoles you are better off not collecting.
Check out the full list from Slash Gear using the link below...

Tech Loadout List
- Manfrotto Advanced 2 Bag
- Apple 2022 MacBook Pro M2
- Sony Alpha ZV-E10
- Sigma 16mm 1.4 sony e mount
- Samsung T7 Portable SSD - 500 GB
- Soundcore by Anker Life Q30 Hybrid Active Noise Cancelling Headphones
- NP-FW50 Battery Charger
- SanDisk USB Drives
- Apple iPhone 13 Pro
- Snug Compact Led2 Powerbank

Introducing The Transparent Turntable & Speakers
The Transparent Turntable is a reinvention of a classic vinyl record player, designed for a modern home and an ever evolving technology.
The Transparent Turntable is meticulously crafted out of aluminium and tempered glass.
It is a belt driven system with a built in phono stage, and a pre-mounted cartridge from Danish Ortofon.
The Transparent Turntable plays music to any sound system, but works best with a Transparent Speaker. It plays with effortless clarity and precision, and offers playback either through cable or Bluetooth.
Check out more via the link below to Transpa.rent ...

Tech Loadout List

Tech Spec List
- Human Centric Workflow Desk
- Human Centric Desk Shelf
- Human Centric Laptop Stand
- Human Centric Storage Drawer for Desk Shelf
- Human Centric Desk Mat
- Human Centric Wrist Rest
- Human Centric Aluminum Headphone Stand
- Elgato Wave Mic Arm LP
- Shure MV7 USB Microphone
- Base One Max MagSafe Charger
- Herman Miller VANTUM GAMING CHAIR
- SanDisk Professional PRO-READER
- Logitech MX Master 3S - Wireless Performance Mouse
- Humanscale Tilting Footrest
- Mode Sonnet Keyboard
- Nanoleaf Lines WiFi Smart RGBW
- BenQ Screen Bar Halo
- BenQ Screen Bar Halo
- Xbox Controller
- Apple 14 inch M1 Pro MacBook
- SanDisk Professional 6TB G-Drive
- Apple AirPods Pro 2
- Apple 27 inch Studio Display
- Apple 27 inch Studio Display
- Apple AirPods Max

Tech Loadout List
- GIGABYTE M32U 32inch Gaming Monitor
- Sony Alpha 7 Camera
- Apple 2022 MacBook Air Laptop
- Logitech Brio 501 Full HD Webcam
- Keychron K3 V2 Wireless keyboard
- Shure MV7 USB Microphone
- Razer Barracuda X Headphones
- Xiaomi Mi Cordless Screwdriver
- Grovemade x Blackwing Pencil Kit
- Orbitkey Nest Desk organizer
- Apple iPhone
- Magsafe Wireless Charger

Tech Spec List
- Shift Standing Desk
- Govee RGBIC Gaming Lights
- Black Color Matte Acoustic Slat Wall Panels
- Fenge Dual Monitor Stand
- Thermaltake Argent E700 Gaming Chair (Glacier White)
- Ekena Millwork WP20X20XAWH 3D Wall Panels
- LACK Wall shelf
- Sanyun SW208 Active Bluetooth 5.0 Bookshelf Speakers
- hunhun U Shape LED Aluminum Channel System
- JOYLIT 24V LED Strip Lights
- Alienware AW3423DW Curved Gaming Monitor
- MAONO Streaming Audio Mixer
- Logitech for Creators Blue Sona Active Dynamic XLR Broadcast Microphone
- Elgato Wave Mic Arm LP White
- Topo White Mousepad
- AMD Ryzen 7 7800X3D 8-Core
- XFX Speedster MERC310 AMD Radeon RX 7900XTX Black Gaming Graphics Card
- ASUS Prime X670E-PRO WiFi Socket AM5 (LGA 1718)
- G.SKILL Trident Z5 RGB Series DDR5 RAM
- JONSBO MOD5 Open Type ATX Mid Tower Gaming Computer Case
- NZXT Kraken Elite 240 RGB
- Elgato Stremdeck
- Xbox Controller
- ASUS ROG Ally
- Razer Tartarus v2
- ASUS TUF Dash F15 FX516 Laptop
- Tablet

Tech Loadout List
- Victorinox Alox Minichamp
- Sofirn HS10 flashlight
- Card wallet
- Samsung galaxy buds 2
- Flipper Zero
- Benchmade Bugout
- Multifunctional Pen
- Carry That Skadis

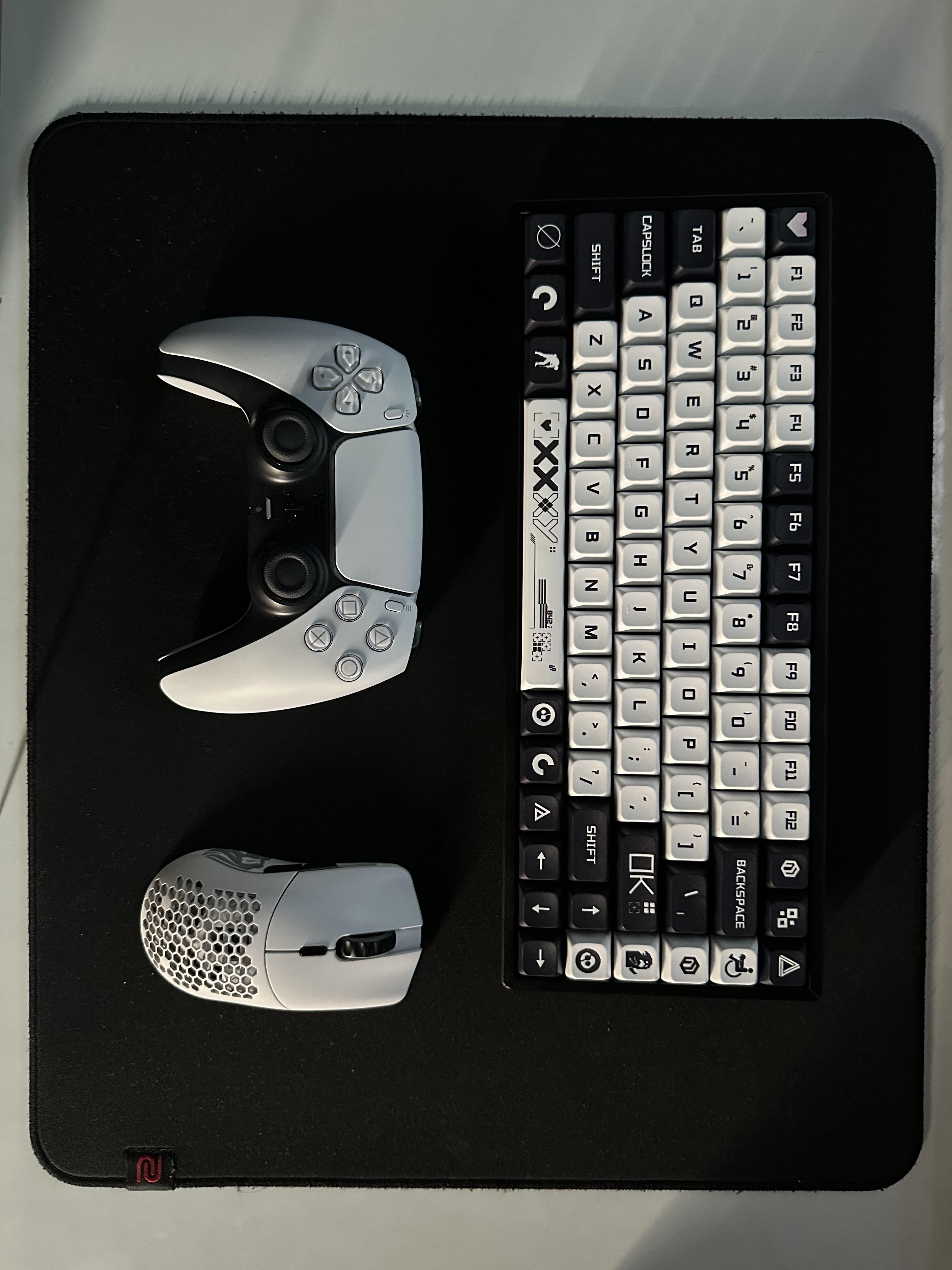
Tech Spec List
- Ryzen 7 5800X
- MSI Gaming Trio RTX 4090
- Asus ROG Crosshair VIII Hero
- Fractal Design North PC Case
- Mountain Everest Max keyboard
- Pwnage Stormbreaker Mouse
- LTT Stealth Mousepad
- Monoprice AHVA WQHD 27inch monitor
- LG Ultragear 48GQ900-B
- Triangle Borea BR03 speakers
- TC-Helicon GoXLR Audio Interface/Mixer
- Schiit Jotunheim 2 Balanced Headphone Amp
- Schiit Bifrost 2 DAC
- NAD C700 DAC/amp
- Audio Technica AT2020 Microphone
- Xbox Wireless Controller
- Nanoleaf Canvas
- Yeelight bedside lamp
- Ikea Alex drawers
- Secretlab Titan 2022 Chair

Tech Loadout List
- MOFT Invisible Slim Laptop Stand
- SAMSUNG SSD T7 Portable External Solid State Drive
- LaCie Rugged SSD 1TB Solid State Drive
- XKM01 Tri-Fold Bluetooth Keyboard
- OXO Good Grips Sweep & Swipe Laptop Cleaner
- UGREEN 100W USB C Charger
- Sony LinkBuds S Truly Wireless Noise Canceling Earbud Headphones
- Logitech MX Anywhere 3 for Mac
- ProtoArc Keyboard Case
- Apple M1 Max MacBook Pro 16
- Moft MS021P-1-BK Jet Black Rotatable Magnetic Laptop Phone Mount
- Belkin iPhone MagSafe Camera Mount

Hand-Held List
- GPD Win 4 Pro 7840U
- ASUS ROG Ally
- ONEXFLY
- AYANEO Air 1S
- AYANEO Geek 1S
- ONEXPLAYER 2 Pro Evangelion
- AYANEO 2S
- Aokzoe A1 Pro 7840U
- GPD Win Max 2 Pro 7840U
Zero Day Alert (Cisco IOS XE)
Posted by CyberTechWare via Cybersecurity & Infrastructure Security Agency
Featured Date: 23/10/2023

Guidance for Addressing Cisco IOS XE Web UI Vulnerabilities
CISA and its partners are responding to active, widespread exploitation of two vulnerabilities, CVE-2023-20198 and CVE-2023-20273, affecting Ciscos Internetworking Operating System (IOS) XE Software Web User Interface (UI).
Organizations running IOS XE Web UI should immediately implement the mitigations outlined in Ciscos Security Advisory. According to the Cisco Talos blog referenced above, a threat actor can:
1. Exploit CVE-2023-20198 to obtain initial access and create a privileged account.
2. Use the privileged account to create a local user account with normal privileges.
3. Using the local user account, exploit another Cisco IOS XE Web UI vulnerability CVE-2023-20273 to inject commands with elevated (root) privileges, which enables the actor to run arbitrary commands on the device.
Mitigation guidance can be found in the CISA link below...
Affliliate Links
Disclaimer
Cybertechware is a tech website that provides its visitors with a curated feed showcasing the latest tech products and gadgets inspired by cyberpunk aesthetics. Our content includes keyboards, mice, screens, speakers, mobile phones, laptops, desktops, and wearable technology. We source our information from various posts on platforms such as YouTube, Reddit, Instagram, Pinterest, and credible news sources.
To support the website financially, we use affiliate marketing links to generate commission sales for some of the items featured on Cybertechware. These include Amazon affiliate links and other third-party affiliates. We may also seek sponsorships in the future as a means of generating revenue. However, it is essential to note that while we strive to provide accurate information and recommendations, we cannot guarantee the quality or performance of any product mentioned on our website. Always conduct your own research before making a purchase decision.
Cybertechware does not endorse or recommend specific products over others; instead, we aim to present a diverse range of options for readers to explore based on their preferences and needs. Any opinions expressed in articles are those of the authors alone and do not reflect the views of Cybertechware as an organization.